The digital heartbeat of modern medicine now pulses through centralized cloud servers, where a single second of unauthorized access can paralyze thousands of clinics and compromise the sanctity of millions of patient records. When CareCloud, a cornerstone of the healthcare technology sector, recently disclosed a network disruption and unauthorized system access, the event sent a clear signal that the industry is facing a transformative crisis of trust. This incident did not just affect a single company in Somerset, New Jersey; it resonated across the 40,000 providers who rely on its artificial intelligence-powered solutions. The breach, which lasted only eight hours before containment, underscores a growing vulnerability in the infrastructure that sustains the American healthcare system. As these platforms generate hundreds of millions in revenue and manage the most sensitive data imaginable, the line between an administrative IT failure and a threat to patient safety has effectively disappeared.
The Current State of Cloud-Based EHR Systems and Digital Healthcare Infrastructure
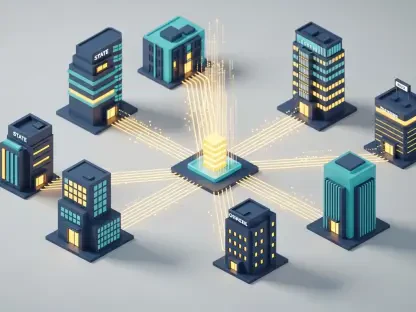
Healthcare technology has moved past the era of local server rooms and paper-stuffed filing cabinets, embracing a sophisticated ecosystem defined by rapid data exchange and predictive analytics. Today, Electronic Health Records serve as the indispensable nerve center for clinical decision-making, billing, and patient engagement. Major market players have successfully migrated the vast majority of American healthcare providers to the cloud, promising seamless interoperability and reduced overhead. However, this transition has fundamentally altered the security equation, moving the perimeter from the hospital walls to the data centers of specialized vendors. This migration has created a landscape where the health of the patient is inextricably linked to the health of the vendor’s network.
The regulatory environment has reacted to these shifts with increased scrutiny, particularly as the Securities and Exchange Commission begins to treat cyber health as a core component of financial stability. While HIPAA remains the gold standard for patient privacy, the newer SEC disclosure requirements highlight the economic gravity of digital infrastructure. Modern healthcare IT is no longer just about storing data; it is about the real-time synthesis of information through artificial intelligence. These interconnected environments drive massive industry growth but simultaneously introduce sophisticated vulnerabilities that traditional security models were never designed to handle. As clinical workflows become more dependent on AI-driven insights, the cost of a system outage is measured not just in dollars, but in the potential for delayed treatments and diagnostic errors.
Evolving Dynamics and Economic Projections for Health IT Security
Emerging Vulnerabilities and Digital Transformation Trends
The rapid integration of artificial intelligence into medical record systems has inadvertently expanded the attack surface available to threat actors. As medical records transition from static files to dynamic data sets that feed diagnostic algorithms, the value of that data increases exponentially on the illicit market. Consumer and provider behaviors are also shifting, with a growing demand for 24/7 accessibility via mobile devices and patient portals. This demand for constant connectivity often conflicts with the necessity of maintaining a rigid security perimeter, creating a tension that hackers are eager to exploit. Interoperability, while essential for coordinated care, often creates centralized points of failure where a single compromised link can lead to a systemic shutdown.
These challenges have inadvertently spurred new opportunities within the cybersecurity market, specifically for specialized forensic advisory and third-party risk management services. As healthcare organizations recognize that they cannot manage these risks in isolation, they are turning to external experts to conduct deep-dive audits and continuous monitoring. The shift toward specialized defense reflects a realization that standard antivirus and firewall solutions are insufficient for a cloud-native environment. Consequently, the industry is seeing a rise in demand for “managed detection and response” services that prioritize active threat hunting over passive alerting.
Market Data and the Future Outlook of Healthcare Cybersecurity
Economic projections for the health IT sector suggest a parallel rise in both the valuation of Electronic Health Record platforms and the spending required to defend them. As the EHR market continues to expand, cyber-defense expenditures are becoming a non-negotiable line item for providers of all sizes. Performance indicators are shifting to prioritize the “cost of downtime” as a primary metric for evaluating IT infrastructure. In many cases, the financial impact of a few days of clinical paralysis far outweighs the annual cost of implementing a robust, multi-layered security framework. This economic reality is forcing a reorganization of budget priorities across the medical landscape.
Looking ahead, the increased oversight from the SEC regarding materiality is expected to foster a new era of corporate transparency. Investors are no longer satisfied with vague assurances of security; they demand detailed reporting on incident response capabilities and the financial resilience of the infrastructure. This pressure for transparency is likely to drive more rigorous security standards across the board as vendors compete not only on software features but on the integrity and availability of their platforms. The long-term impact will likely involve a consolidation of the market around vendors who can prove their resilience through independent audits and transparent disclosure practices.
Addressing the Challenges of Third-Party Concentration and Systemic Risk
The CareCloud incident vividly illustrates the “Cascade Effect,” where a single point of failure within a major vendor’s environment can disrupt care for thousands of independent medical practices simultaneously. This concentration risk means that a localized breach is never truly local in its consequences. When one of the six primary EHR environments was accessed, the impact was felt by a significant portion of the provider base, highlighting how dependency on a few major players creates a fragile ecosystem. To combat this, the industry must move away from “Passive Dependency,” where providers assume a vendor’s security is infallible. Active oversight, including regular security posture reviews and participation in joint incident response drills, is becoming the new standard for diligent medical practice management.
Overcoming these technological hurdles requires balancing the push for rapid software deployment with the need for exhaustive security testing. In a market where new features and AI integrations are rolled out weekly, the window for vulnerability testing is often dangerously narrow. Mitigation strategies are now focusing on the implementation of localized downtime procedures that allow a clinic to function even when its primary cloud provider is offline. Diversifying EHR environments or maintaining offline caches of critical patient data provides a safety net that can prevent a digital breach from becoming a clinical catastrophe.
The Regulatory Landscape and the Materiality of Patient Privacy
The legal framework governing healthcare technology is undergoing a significant evolution, with laws and standards now emphasizing the “materiality” of cyber events. When a public company like CareCloud files an SEC notification, it signifies that the breach has reached a threshold where it could reasonably affect the decisions of a prudent investor. This evolution marks a shift from checkbox auditing to a more dynamic, real-time threat detection and reporting model. Compliance is no longer a static goal achieved once a year; it is a continuous state of readiness.
Cyber insurance carriers are also playing a pivotal role in shaping these industry standards. By mandating specific security measures as a condition for coverage, these carriers are effectively acting as private-sector regulators. Vendors who fail to meet these evolving requirements find themselves facing higher premiums or even a total loss of coverage, which in turn impacts their ability to attract large-scale healthcare clients. The legal and financial consequences of a breach are no longer limited to immediate remediation costs. Long-term impacts include the potential for massive class-action litigation and significant regulatory fines, both of which can linger on a company’s balance sheet for years after the initial intrusion was contained.
The Future of Resilient Health IT Systems and Vendor Partnerships
Innovation in the sector is moving toward a “Trust but Verify” model, where the relationship between a healthcare provider and an IT vendor is defined by continuous monitoring rather than a one-time contract. Integrated scenario exercises, where both parties simulate a total system failure, are becoming common practice. These exercises ensure that when a real breach occurs, the response is instinctive and coordinated. Beyond organizational changes, potential market disruptors like blockchain and decentralized data storage are gaining traction as alternatives to the current centralized cloud model. By distributing data across a network rather than storing it in a few massive silos, the impact of a single breach could be significantly mitigated.
The ultimate goal of these innovations is to prioritize patient safety and clinical continuity during active breaches. Future systems are being designed with built-in redundancies that protect the integrity of the data even if the availability is temporarily compromised. In an era where international cyber threats are influenced by global economic and political factors, domestic healthcare security policies must remain agile. The intersection of global threat intelligence and localized clinical care is the next frontier for health IT, requiring a level of collaboration between the public and private sectors that has yet to be fully realized.
Lessons from the CareCloud Incident and Strategic Recommendations
The findings from the CareCloud breach demonstrated that the critical intersection of data privacy, clinical safety, and institutional resilience required more than just technical solutions. Stakeholders realized that transparent communication served as the most effective tool for minimizing patient risk during an active disruption. The industry learned that early notification allowed clinics to pivot to emergency protocols before patient care was impacted, proving that the speed of information was as vital as the speed of the forensic investigation. Organizations that prioritized openness over reputation management were better positioned to maintain the long-term trust of their providers and patients.
Strategic recommendations for the future included the implementation of more rigorous due diligence processes that went beyond a vendor’s technical specifications. Contractual safeguards were updated to include specific limitations of liability and clear mandates for business continuity that aligned with the volume of patient data under management. The industry moved toward a model where healthcare providers actively participated in the security ecosystem rather than remaining passive consumers of technology. This shift in perspective fostered a more resilient environment where the inevitability of cyber threats was met with a robust, multi-layered defense strategy. Ultimately, the reevaluation of vendor partnerships focused on creating a culture of shared responsibility that placed the safety of the patient at the center of every digital transaction.